FortiGate Outbound Static NAT using IP Pools v5.4
Say you have a block of static IP addresses from your provider. You are using one of them for the external IP address of your FortiGate, this is typically applied as the NAT address for your inside traffic to access the Internet.
If you have an internal server that you want to use one of your other static IP addresses instead this is the process for you. This is commonly done for something like an internal mail server that you always want to appear as if it’s traffic is coming from the same static public IP address, different then the external IP address on your firewall.
For this example, our external IP address on the firewall is 1.1.1.1. The public IP address we want to apply to our mail server is 1.1.1.2. The inside IP address of the mail server is 2.2.2.5.
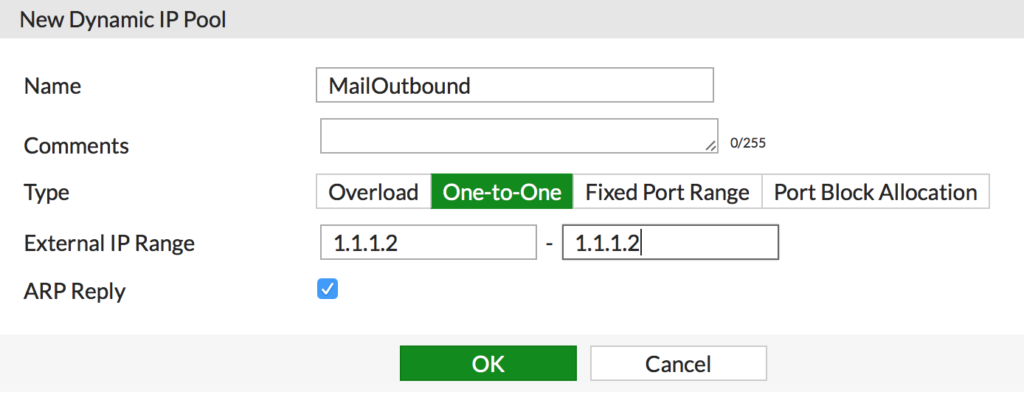
Create IP Pool
First we have to create the IP Pool, or one-to-one NAT pool.
- Navigate to Policy & Objects > IP Pools and click Create New
- Enter a descriptive name, click One-to-One and enter the external IP address you want applied for this pool
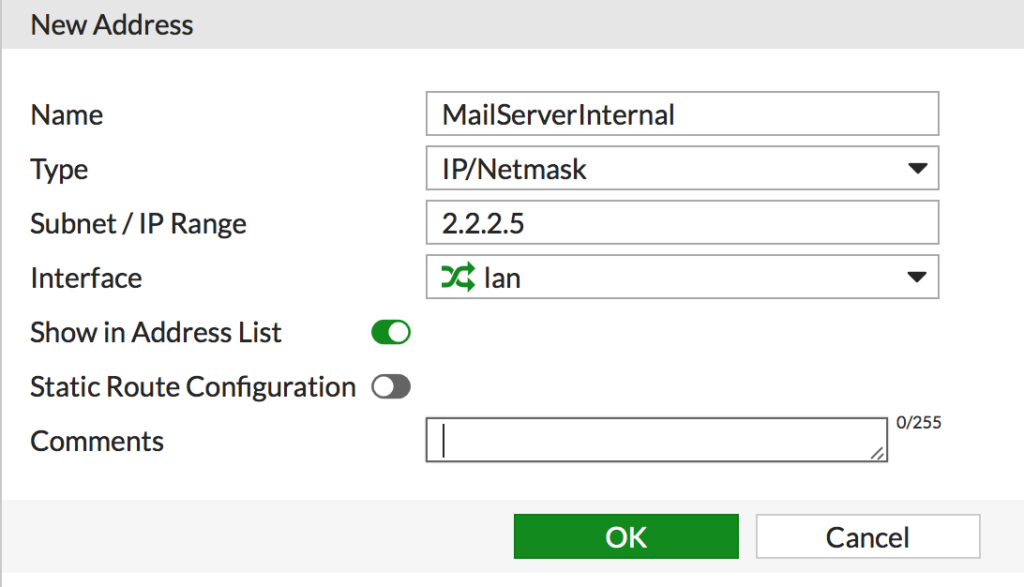
Create Address Object for the mail server
- Navigate to Policy & Objects > Addresses and click Create New
- Give the object a descriptive name, set the inside IP address of the server and the interface and click OK
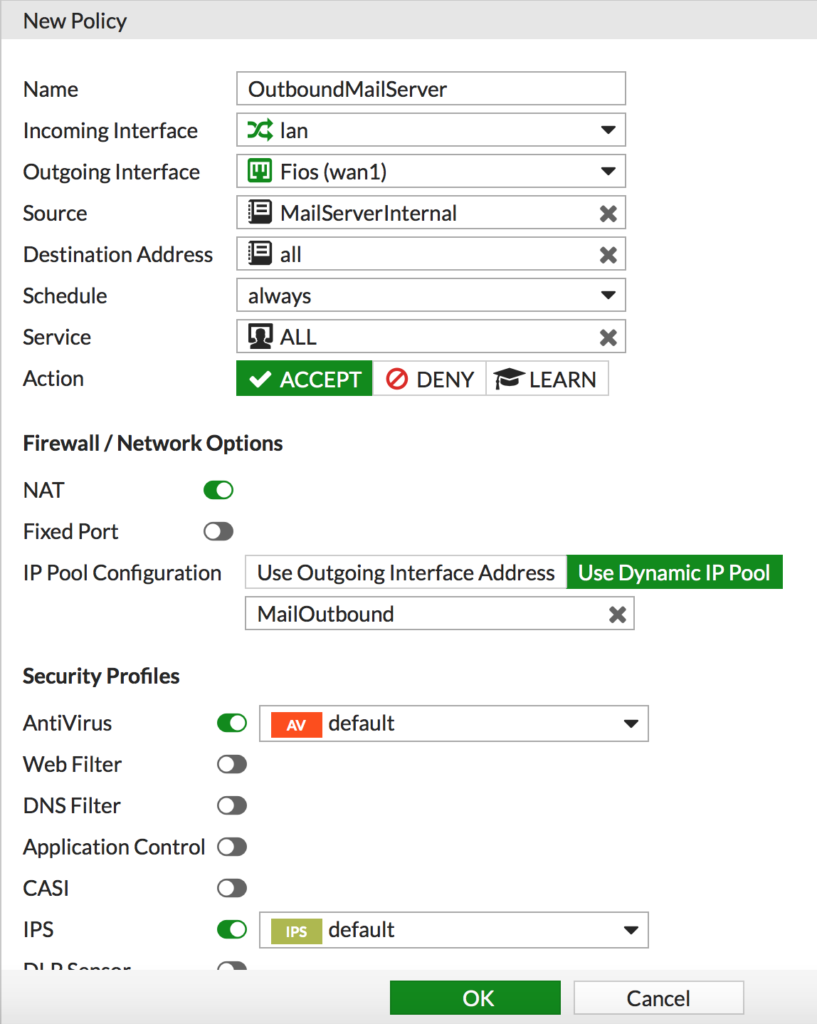
Create IPv4 Policy
Finally we create a policy for our mail server.
- Navigate to Policy & Objects > IPv4 and click Create New
- Populate the new rule
- Name: Give it a descriptive name
- Incoming Interace: Your inside network the server is on
- Outgoing Interface: The outside interface the traffic will use
- Source: The Address Object created for the mail server
- Destination Address: All
- Service: All
- Make sure NAT is enabled
- Change the IP Pool Configuration to Use Dynamic and select the IP Pool you created earlier
- Enable whatever security profiles you want for this connection and click OK
If you have VIP’s setup for inbound access, you can add the IP Pool to the existing security policy rather then creating a new one.
Check out this related post, FortiGate Inbound Port Forwarding using VIP’s v5.4